

DevSecOps in 2026: Tools, Frameworks, and Best Practices for Security






Software development has become faster and more automated than ever. Teams push updates frequently, release new features quickly, and rely heavily on CI/CD pipelines to stay competitive. Speed is no longer optional; it has become a basic expectation for modern software teams.
When security is not part of the development process, speed can easily turn into risk. A small flaw in the code or a wrong configuration can pass through the pipeline without anyone noticing. By the time it reaches production, the damage may already be done.
This can lead to data breaches, compliance failures, downtime, and loss of customer trust. Fixing these issues after release is significantly more expensive and disruptive than preventing them during development.
DevSecOps addresses this challenge by embedding security into every stage of the software development lifecycle. Security is not treated as a final checkpoint. It becomes a continuous practice from planning and coding to testing and deployment.
DevSecOps tools support this approach by integrating directly into CI/CD workflows. They automate code analysis, dependency scanning, and compliance checks, helping teams detect and resolve risks early without slowing delivery.
In this blog, you will learn what DevSecOps is, what it offers, and the 15 essential practices to secure your pipeline in 2026, along with the key tools and frameworks that support a strong DevSecOps strategy.
DevSecOps is an approach that brings security into every stage of the DevOps lifecycle. In a traditional DevOps model, development and operations teams work together to release software faster. Security is often reviewed at the end. This delay can lead to last-minute fixes, higher costs, and release slowdowns.
It changes this by adding security from the beginning of the software development lifecycle. This is often called shifting security left. Instead of finding problems after deployment, teams identify and fix them as they write and build the code. The result is safer software without slowing down delivery.
The benefits of DevSecOps are practical and measurable:
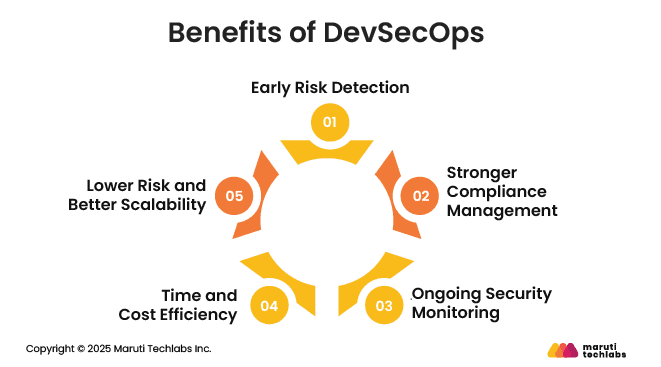
Security checks start during development. Vulnerabilities are identified while the code is being written and built, making them easier and faster to fix.
When security is built into the pipeline, meeting standards such as PCI DSS, HIPAA, GDPR, and ISO becomes simpler. Compliance is maintained continuously rather than handled at the last minute.
Security testing runs automatically within CI/CD workflows. Teams can detect issues in real time instead of waiting for post-deployment reviews.
Fixing problems early reduces rework and avoids long security approval cycles. Teams save time, reduce costs, and release updates with fewer delays.
Continuous checks reduce the likelihood that vulnerabilities reach production. As systems grow, security practices scale with them, enabling stable, secure expansion.
Securing your CI/CD pipeline in 2026 requires more than adding a few security tools at the end. DevSecOps works well when security is not treated as a separate task. It becomes part of how the team builds software every day. The goal is simple: create secure applications without slowing down progress.
The practices below help teams lower risk, work better together, and continue delivering updates at a steady pace.
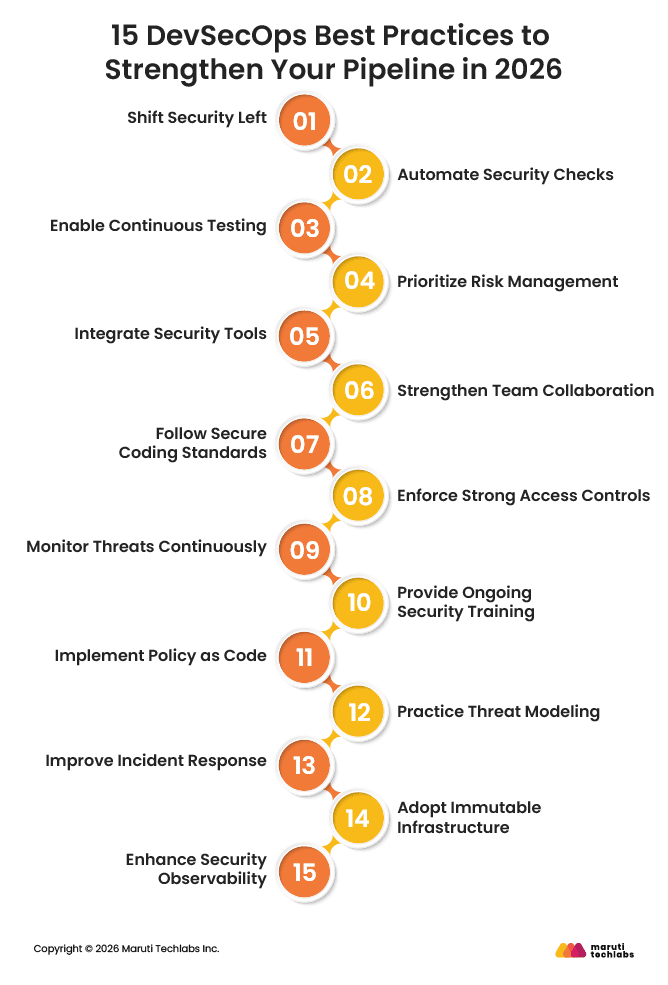
Security should not wait until the code is complete. It needs to begin at the moment a feature is planned. If teams discuss possible risks early, they can avoid many problems later.
When developers understand what could go wrong, they write better and more careful code. This reduces last-minute surprises before release. It also prevents long delays caused by fixing issues that should have been caught earlier.
Security automation ensures that every code change is scanned consistently without relying on manual intervention. Automated tools analyze source code, dependencies, containers, and configurations at predefined stages in the pipeline. This guarantees uniform enforcement of security policies and reduces human error.
Security testing should run continuously throughout the development lifecycle, not just at specific checkpoints. By integrating testing into every build and deployment cycle, teams can detect vulnerabilities as features evolve, preventing small issues from escalating into major risks.
Not every vulnerability needs immediate action. Teams should focus on high-risk issues that could cause serious damage. A risk-based approach helps allocate time and resources wisely.
Security tools must fit naturally into development workflows. Code scanning, container security checks, and infrastructure testing should run within the CI/CD pipeline to detect issues automatically.
DevSecOps works only when everyone takes responsibility for security. It is not just the security team’s job. Developers, operations, and security teams need to stay aligned and maintain open communication.
When teams stop working in isolation and share ownership, releases move faster, and security improves naturally.
Simple and clear coding guidelines make a big difference. When developers know what to follow, they are less likely to repeat common mistakes.
Regular code reviews also help. They give teams a chance to spot weak areas early and improve the overall quality of the application before it moves ahead.
Limit access to systems and data based on roles. Apply the principle of least privilege so that users and services have only the permissions they truly need. This reduces the risk of misuse or breaches.
Continuous monitoring provides visibility into system activity. Reviewing logs, tracking network behavior, and setting up alerts help teams detect unusual patterns before they turn into serious incidents.
Security awareness is essential. Regular training helps developers understand new threats, common vulnerabilities, and secure coding techniques. Educated teams make fewer mistakes.
Define security policies in code form so they can be applied automatically across environments. This ensures consistent enforcement of standards without relying on manual checks.
Before building a feature, take a moment to think about how someone might try to misuse it. This simple exercise helps teams spot weak points early and add the right protections before the feature goes live.
Even strong systems can face security events. Teams should create clear response plans and regularly test them. A prepared team can reduce downtime and limit damage during an incident.
Instead of modifying live systems, replace them with updated and pre-configured versions. This reduces configuration errors and improves deployment consistency.
Better visibility leads to faster decisions. Advanced monitoring and reporting tools provide teams with clear insights into performance and security, enabling them to respond quickly to potential risks.
When these practices are applied together, DevSecOps becomes a strong foundation for secure, scalable, and reliable software delivery in 2026.
DevSecOps is not just about teamwork and processes. It also depends on using the right tools.
These tools automate security checks, monitor systems, and support developers across the pipeline. When they work together, security becomes part of the daily workflow instead of an extra step at the end.
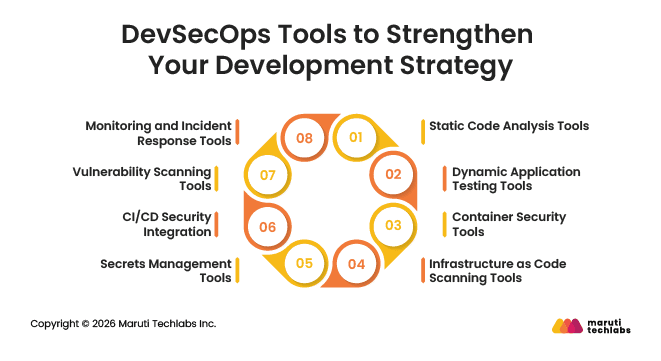
Static Application Security Testing tools review source code while it is being written. They help identify insecure coding patterns, hardcoded credentials, and common vulnerabilities early in the development cycle.
Dynamic testing tools check applications while they are running. They simulate real-world attacks to uncover issues such as broken authentication or injection flaws.
As containers become common, security tools scan container images for known vulnerabilities and configuration weaknesses before deployment.
These tools review infrastructure templates to detect misconfigurations that could expose systems to risk. They help ensure secure cloud and server setups.
Secrets management solutions store and protect sensitive data such as API keys, passwords, and tokens. They prevent credentials from being exposed in code.
Modern CI/CD platforms allow security tools to run automatically at each stage of the pipeline. This ensures consistent and repeatable security checks.
These scanners examine applications, networks, and dependencies to find weaknesses that attackers might exploit.
Monitoring tools provide real-time visibility into system activity. They help teams detect threats quickly and respond before major damage occurs.
Using these tools together creates a balanced, reliable DevSecOps setup that supports secure, steady software delivery.
There is no single DevSecOps framework that works for every team. Each framework solves different problems, so the real question is which one fits your team’s workflow, risk tolerance, and regulatory needs.
Most teams in 2026 already have CI/CD pipelines, cloud platforms, and some security tools in place. Choosing a framework is less about following one entirely and more about picking guidance that sets rules and fills the gaps in your process.
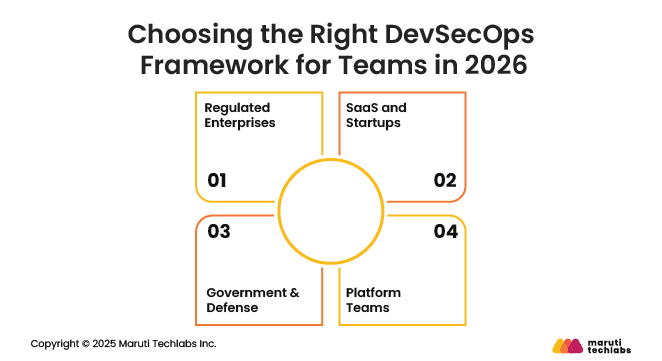
Teams in highly regulated industries often follow NIST SSDF. It gives clear expectations for audits and compliance reviews. The challenge is to translate those rules into practical controls that work within your CI/CD pipeline.
For SaaS companies and growing startups, OWASP DevSecOps guidance is a natural fit. It works well with CI/CD workflows and lets teams introduce security controls gradually as automation and processes mature, without adding heavy upfront procedures.
Government and defense teams usually start with NIST guidance and add additional control catalogs to meet strict compliance and security standards. This ensures all requirements are covered while remaining practical for daily development.
Platform teams usually mix and match frameworks to cover all their needs. OWASP guides how security works in CI/CD, SLSA protects builds and artifacts, and NIST sets the basic standards everyone must meet. The tricky part is keeping these pieces working together as teams and platforms change over time.
At the end of the day, the best framework is the one your team can actually use every day. It should be easy to explain to engineers, auditors, or leadership and reliable enough for the team to trust. The goal isn’t to pick the most popular framework, but the one that truly fits your team’s way of working.
DevSecOps is about making security a natural part of the entire development process. From planning and coding to testing and deployment, it ensures vulnerabilities are caught early, risks are managed, and software is delivered safely without slowing down innovation. Practices like shifting security left, continuous testing, automated checks, and strong collaboration help teams build reliable, secure applications while maintaining speed and agility.
Choosing the right tools and frameworks further strengthens the pipeline, allowing teams to monitor systems, enforce standards, and respond quickly to potential threats. Every organization, whether a regulated enterprise, SaaS company, government team, or platform team, can adapt DevSecOps to fit its needs and priorities.
If you want to secure your development pipeline and deliver software confidently, Maruti Techlabs can help. Explore our DevSecOps services and reach out through our Contact Us page to get started.
DevSecOps is a way of working that integrates security into every stage of software development. Instead of adding security at the end, it is considered from planning, coding, testing, and deployment. The goal is to deliver secure software faster while reducing risks and preventing vulnerabilities before they reach production.
A DevSecOps pipeline is a development workflow that combines DevOps practices with automated security checks. It includes code building, testing, deployment, and monitoring, with security tools running at each stage. This ensures vulnerabilities are detected early, compliance is maintained, and software is delivered reliably and safely.
To implement DevSecOps, start by shifting security left, introducing automated testing, and using tools to scan code, containers, and infrastructure. Train teams on secure coding, enforce access controls, and integrate security policies into CI/CD pipelines. Continuous monitoring and collaboration between developers, operations, and security teams is essential.
DevSecOps best practices can face challenges such as high upfront setup costs, tool complexity, and resistance from teams unfamiliar with integrated security. It may require cultural change, ongoing training, and careful selection of frameworks. Security gaps can still appear if automation or monitoring is not properly configured or maintained.


