

What Is Application Security and Why Do Modern Enterprises Need It?






As software systems become more complex and cyber threats continue to evolve, application security is no longer optional for modern enterprises. With cloud adoption, microservices, rapid development cycles, and growing mobile app security needs, applications are expanding quickly, making them harder to secure. Without the right security practices in place, businesses risk data breaches, compliance issues, and long-term reputational damage.
Recent reports highlight a growing concern: while 92% of organizations are using AI coding tools, nearly 81% still lack visibility into AI-generated code. This makes it one of the biggest blind spots in application security today.
In this blog, we’ll walk through what application security is, why it matters, common risks enterprises face, key best practices, and how continuous monitoring helps prevent threats.
Application security is the practice of protecting software applications, their code, and the data they handle from both internal and external threats. It includes a set of processes, tools, and best practices applied throughout the entire software lifecycle—from development to deployment. The goal is to identify, fix, and prevent vulnerabilities before attackers can exploit them.
As modern applications become more complex, especially with cloud-native architectures and open-source dependencies, the risk surface continues to grow. Businesses are relying more on digital systems, which makes applications a primary target for cyberattacks. This makes application security a critical part of any enterprise strategy rather than just a technical requirement.
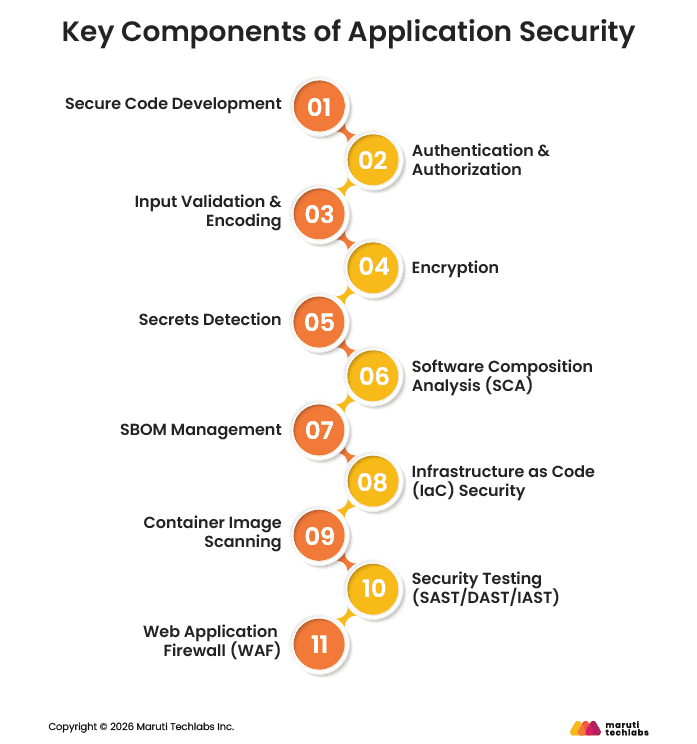
Key components of application security include the essential practices used to protect applications, code, and data from threats. These areas work together to reduce vulnerabilities, secure access, and ensure continuous protection across the application lifecycle.
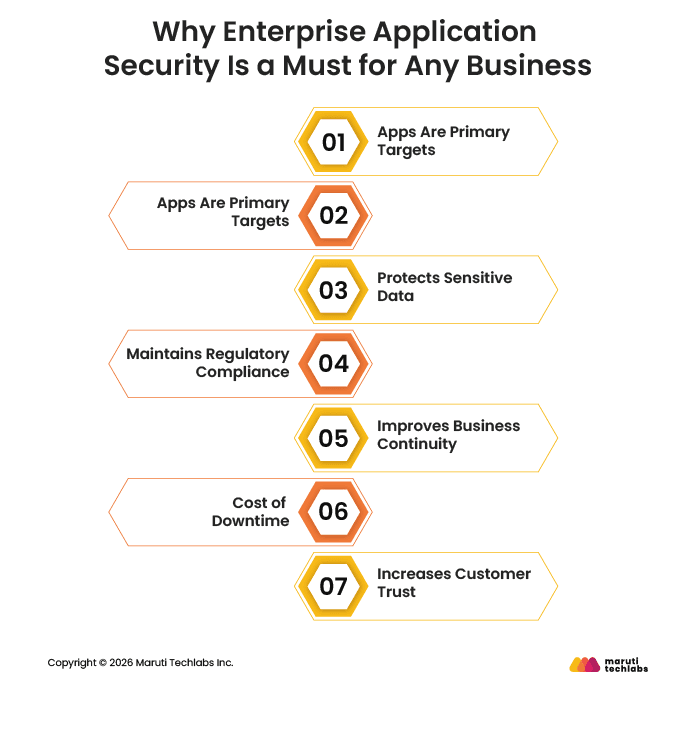
Enterprise application security is critical because applications are central to business operations and handle sensitive data. Even a small vulnerability can lead to serious financial, operational, and reputational impact, with the average data breach costing around $4.4 million. A proactive approach helps businesses reduce risks, avoid downtime, and maintain trust.
The most common application security risks for enterprises in 2025–2026 come from the growing complexity of modern systems, including AI usage, widespread APIs, and heavy reliance on third-party components. These setups create many entry points, where even small gaps can turn into serious vulnerabilities. That’s why enterprises need to clearly understand these risks to better protect their applications and reduce overall exposure.
Below are some of the most common application security risks and why they matter:
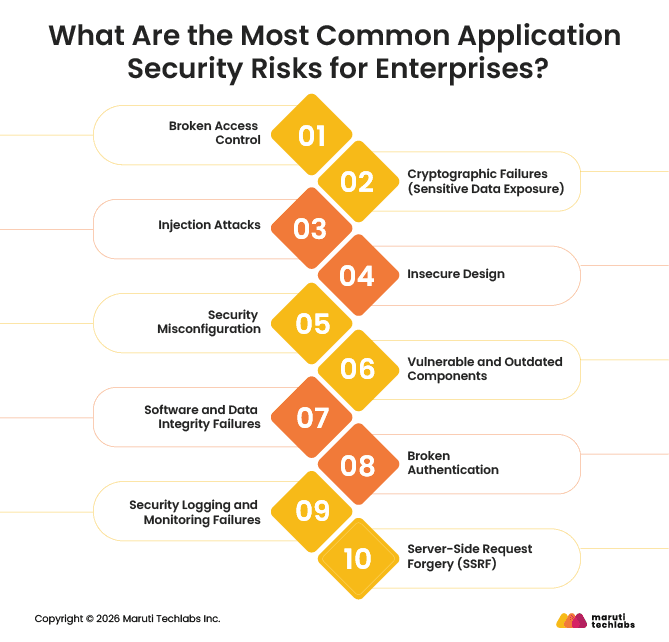
Broken access control happens when users can access data or actions they are not supposed to. This usually occurs when permissions are not properly enforced across the application. It can allow attackers to view or modify sensitive information.
This risk can lead to unauthorized access to critical systems or data. For example, a normal user might gain admin-level access and change important settings. Such issues can directly result in data leaks or system misuse.
This risk occurs when sensitive data is not properly protected using encryption. It can happen due to weak algorithms, poor key management, or no encryption at all. As a result, confidential data becomes easy to access.
Attackers can intercept or steal sensitive information like passwords or financial data. For example, if user data is stored in plain text, it can be easily read after a breach. This leads to serious privacy and compliance issues.
Injection attacks happen when untrusted input is treated as a command by the system. This includes attacks like SQL injection or script injection. Attackers use this to manipulate databases or execute harmful commands.
It allows attackers to control application behavior or access restricted data. For example, a malicious input in a login field could expose the entire database. This can compromise both data and system integrity.
Insecure design refers to flaws that exist because security was not considered during planning. These issues are part of the application’s structure and are harder to fix later. They often lead to long-term vulnerabilities.
Poor design decisions can expose the system to multiple attack paths. For example, missing validation checks in workflows can allow unauthorized actions. Fixing these issues later usually requires major changes.
Security misconfiguration happens when systems are set up incorrectly or left with default settings. This includes open ports, unused features, or weak permissions. It is very common in cloud-based environments.
Attackers can easily find and exploit these gaps. For example, a public cloud storage bucket can expose sensitive files. Such mistakes often lead to avoidable data breaches.
Applications often use third-party libraries and frameworks to function. If these components are outdated or unpatched, they may contain known vulnerabilities. Attackers actively look for such weaknesses.
Known vulnerabilities are easy targets because fixes are already documented. For example, using an old library with a public exploit can give attackers quick access. Regular updates are essential to reduce this risk.
This risk occurs when applications do not verify the integrity of code or data. It can allow attackers to introduce tampered updates or malicious code. This is especially risky in automated deployment pipelines.
Attackers can inject harmful code without being detected. For example, a compromised software update can spread malware across systems. This can impact multiple users and systems at once.
Broken authentication happens when login systems are weak or poorly managed. This includes issues like weak passwords or improper session handling. It makes it easier for attackers to impersonate users.
Attackers can gain access using stolen or guessed credentials. For example, lack of multi-factor authentication increases the chances of account takeover. This can lead to unauthorized actions and data exposure.
This risk occurs when systems do not properly track or monitor security events. Without logs, it becomes difficult to detect or investigate attacks. Many breaches go unnoticed due to this gap.
Delayed detection increases the damage caused by an attack. For example, an attacker may stay undetected in a system for weeks. Proper monitoring helps teams respond quickly and reduce impact.
SSRF happens when a server makes requests to unintended locations based on user input. This occurs when input URLs are not properly validated. It can expose internal systems that are otherwise protected.
Attackers can use the server to access internal services or sensitive data. For example, they may retrieve confidential information from internal APIs. This can lead to deeper system compromise.
Application security best practices include a set of measures that help protect applications from development to deployment and beyond. These practices focus on secure coding, access control, data protection, dependency management, and continuous monitoring. Together, they help reduce vulnerabilities, prevent attacks, and maintain a strong security posture.
Secure coding ensures that applications are built with security in mind from the start, supporting a shift-left security approach within DevSecOps practices. It includes input validation, code reviews, and avoiding common vulnerabilities. This helps reduce issues early in the development lifecycle.
Fixing vulnerabilities during development is easier and less costly than after deployment. For example, validating user input can prevent attacks like SQL injection or XSS. This reduces the chances of exploitable flaws reaching production.
IAM focuses on controlling user access and ensuring only authorized users can interact with systems. It includes authentication, authorization, and role-based access controls. This limits unnecessary access across applications.
Restricting access reduces the risk of unauthorized actions. For example, giving users only the permissions they need prevents misuse of sensitive data. This helps avoid privilege escalation and data breaches.
This practice ensures that sensitive data is properly secured using encryption methods. It protects data both when stored and when being transferred. This keeps critical information safe from exposure.
Encrypted data cannot be easily read even if intercepted. For example, using encryption for user credentials protects them during transmission. This reduces the impact of potential data breaches.
APIs need to be secured to prevent unauthorized access and misuse. This includes validating requests, controlling access, and monitoring traffic. Proper API security helps protect connected systems.
Unsecured APIs can expose sensitive data or system functions. For example, missing authentication on an API can allow attackers to extract data. Securing APIs helps prevent such direct access risks.
Modern environments use containers, infrastructure as code, and serverless functions. These components must be configured securely to avoid vulnerabilities. Proper setup reduces risks across cloud environments.
Misconfigurations in these components are a common cause of breaches. For example, an exposed cloud configuration can allow public access to data. Securing them helps reduce the overall attack surface.
Applications rely on third-party libraries and dependencies. Keeping them updated ensures known vulnerabilities are patched. This is essential for maintaining a secure environment.
Outdated components are easy targets for attackers. For example, using a library with a known vulnerability can lead to quick exploitation. Regular updates help prevent such risks.
Monitoring applications during runtime helps detect threats as they happen. It involves tracking activity, analyzing logs, and identifying unusual behavior. This ensures ongoing protection after deployment.
Real-time monitoring helps detect and respond to attacks quickly. For example, unusual login activity can signal a potential breach. Early detection reduces damage and downtime.
Dynamic testing evaluates applications while they are running. It helps identify vulnerabilities that may not appear during development. This adds an extra layer of security validation.
Some issues only appear in real-world conditions. For example, runtime misconfigurations can be detected through DAST. This helps uncover hidden vulnerabilities before attackers do.
Regular audits and testing help evaluate the effectiveness of security measures. Penetration testing simulates real attacks to find weaknesses. This ensures security practices stay effective over time.
New vulnerabilities can appear as systems evolve. For example, a penetration test can reveal hidden flaws missed by automated tools. Regular testing helps keep applications secure against new threats.
Application security monitoring helps detect and prevent threats by continuously tracking how an application behaves during runtime. It gives real-time visibility into what’s happening inside the application, helping detect risks that traditional tools often miss. This allows teams to quickly identify and respond to potential threats.
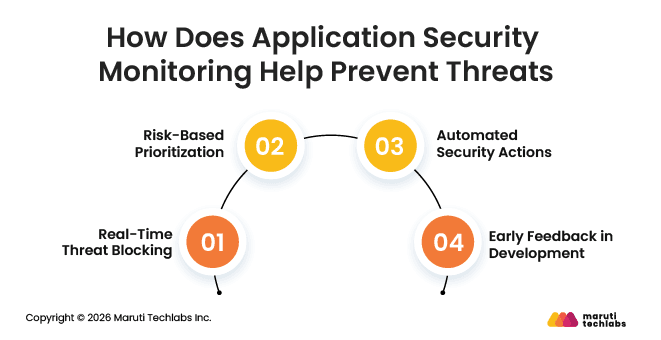
Monitoring tools analyze application behavior to detect unusual or risky activities. They go beyond surface-level checks and focus on what is happening inside the application. This helps uncover hidden threats early.
Application security monitoring also plays a key role in preventing threats before they cause damage. It enables quick action and helps teams focus on the most critical risks. This improves overall security response.
Application security is not a one-time task but an ongoing effort that needs continuous attention. As applications grow and threats evolve, businesses must keep improving their security practices using the right tools, processes, and skilled teams.
Strong application security helps reduce risks, prevent costly breaches, and keep systems running smoothly. With the right cybersecurity support, businesses can identify gaps early and build a more secure and reliable application environment.
Maruti Techlabs helps businesses strengthen application security with a focused and practical approach. Our team works closely with organizations to identify risks, improve application performance, and ensure security is built into every stage of development.
Our expertise covers secure development, risk assessment, and modern cloud environments. Businesses looking to enhance protection can explore our Application Security Services, while those planning a stronger foundation can benefit from our Security Architecture & Advisory Services.
In one of our engagements, we supported a leading Business Intelligence (BI) platform facing performance and scalability issues as its user base grew. Legacy features, slow platform speed, and unoptimized code were affecting user experience, while maintaining security and compliance added to the challenge.
Through structural improvements and feature redesigns, we helped enhance performance and create a stronger base for future growth. If you're working on a similar challenge, you can talk to our experts about your project.
Application security is the practice of protecting software applications from threats and vulnerabilities throughout their lifecycle. It involves using tools, processes, and best practices to secure code, data, and user interactions. The goal is to prevent unauthorized access, data breaches, and attacks that can compromise application functionality and user trust.
Application security is important because applications handle sensitive data and are common targets for cyberattacks. Weak security can lead to data breaches, financial losses, and reputational damage. Strong security measures help protect user information, ensure compliance with regulations, and maintain smooth business operations without disruptions caused by security incidents or attacks.
The future of application security will focus on automation, AI-driven threat detection, and stronger integration within development processes. As applications become more complex, security will shift earlier in development and continue through runtime. Businesses will rely on continuous monitoring and intelligent tools to identify and prevent evolving threats more effectively and efficiently.
Application security and network security are different but related. Application security focuses on protecting software and its code from vulnerabilities, while network security protects the underlying infrastructure and communication channels. Both are essential, but application security specifically addresses risks within applications where most modern cyberattacks are targeted today.
Application security is implemented by integrating security practices across the software development lifecycle. This includes secure coding, code reviews, automated testing, encryption, access control, and continuous monitoring. Organizations also use tools like SAST, DAST, and SCA to detect vulnerabilities early and ensure applications remain secure during development and after deployment.
In DevOps, application security ensures that security is integrated into fast-paced development and deployment processes. Known as DevSecOps, it includes automated testing, secure coding, and continuous monitoring within CI/CD pipelines. This approach helps teams identify and fix vulnerabilities early without slowing down development or compromising application performance and delivery timelines.
Common challenges include managing complex application environments, securing third-party dependencies, and keeping up with evolving threats. Limited visibility into systems and a lack of skilled resources can also create gaps. Additionally, balancing security with fast development cycles makes it difficult for teams to implement strong security without affecting speed and productivity.
Application security directly impacts user trust by ensuring that personal and sensitive data is protected. A secure application shows users that their information is handled responsibly. On the other hand, security breaches can damage reputation and reduce confidence. Strong security practices help build trust, improve user experience, and maintain long-term customer relationships.


