Secure Cloud Architecture: Core Principles for Enterprise Security






Cloud adoption continues to grow, but securing cloud environments has become more challenging than ever. In most enterprise setups, cloud misconfigurations are almost unavoidable, and security teams fix many of them every day. The challenge is that attackers can detect and exploit these weaknesses within minutes, sometimes before security teams can respond.
At the same time, organizations increasingly use Infrastructure as Code (IaC) to build and manage cloud infrastructure through APIs. While this speeds up development, it also introduces constant changes that can create new misconfigurations. As a result, the cloud control plane that manages configurations and access through APIs becomes a critical area to protect.
This growth in cloud adoption is expected to continue in the coming years. According to IDC, 84.1% of AI infrastructure spending in 2Q25 was in cloud and shared environments, highlighting the growing reliance on cloud platforms. As these environments expand, organizations must strengthen their cloud security architecture and follow best practices to stay protected.
In this blog, we will discuss what secure cloud architecture entails, the security risks enterprises must address, and the best practices organizations can follow to build resilient, secure cloud environments.
Cloud security architecture is the framework that protects cloud data, applications, and infrastructure. It acts as a structured blueprint that defines how security controls are designed and implemented across a cloud environment. As organizations move critical workloads to the cloud, relying on traditional security approaches is no longer enough.
Cloud environments change frequently, and every change can introduce potential risks. A well-designed cloud security architecture helps organizations manage these risks by building security directly into the cloud environment.
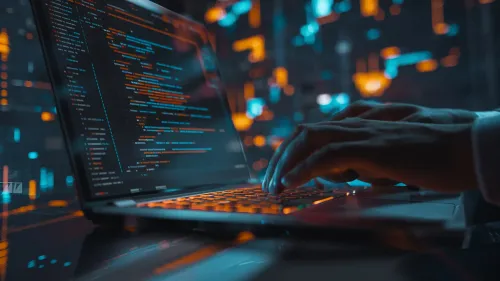
A secure cloud architecture includes five core components—IAM, Data Security, Network Security, Application/Workload Security, and Compliance/Monitoring—designed to protect cloud systems, applications, and data.
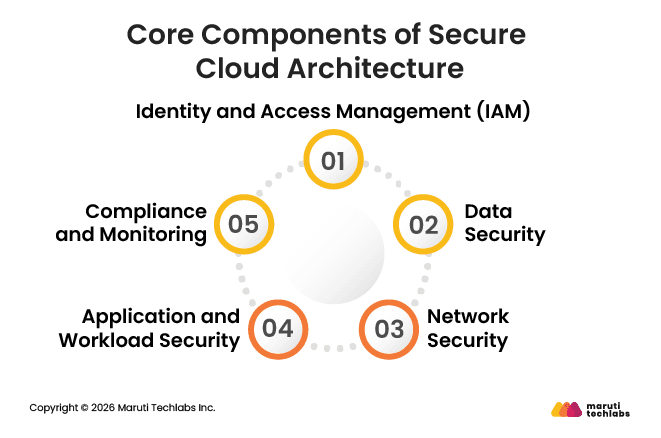
A well-structured cloud security architecture delivers benefits such as protection against breaches, regulatory compliance, customer trust, business continuity, and secure scalability, strengthening enterprise cloud operations.
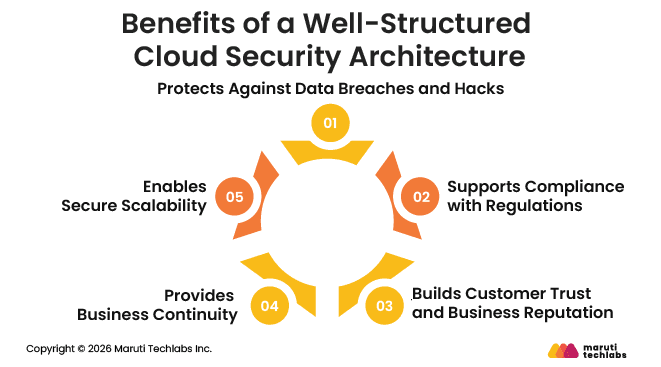
Enterprise cloud environments face risks such as data exposure, compromised accounts, unsecured APIs, misconfigurations, insider threats, and limited visibility. Addressing these risks is essential to protect systems, ensure compliance, and maintain secure cloud operations.
Data breaches remain one of the biggest risks in cloud environments. They often occur when sensitive data is stored without proper encryption or weak access controls. Misconfigured cloud systems can expose confidential information to unauthorized users.
For example, in 2025, the ShinyHunters group exploited misconfigured Salesforce and Snowflake cloud environments globally, exposing sensitive customer and business data across hundreds of organizations, showing how cloud misconfigurations can have widespread consequences.
Attackers may gain access to cloud accounts by stealing credentials through phishing or brute-force attacks. Once an account is compromised, attackers can manipulate data, deploy malicious programs, or even use cloud resources for activities such as cryptocurrency mining.
Application Programming Interfaces (APIs) allow cloud services and applications to communicate with each other. If APIs are not properly secured or authenticated, attackers can exploit them to access systems or extract sensitive data.
Denial of Service attacks occur when attackers overwhelm cloud applications or services with excessive traffic. This can make systems unavailable to legitimate users and disrupt important business operations.
Security threats do not always come from outside the organization. Employees or contractors with legitimate access can accidentally expose data or intentionally misuse their privileges.
Misconfiguration is one of the most common causes of cloud security incidents. Improper settings, such as publicly accessible storage buckets or weak firewall rules, can expose systems and sensitive data.
Poor Identity and Access Management practices, such as excessive permissions or a lack of multi-factor authentication, can allow unauthorized users to gain access to cloud systems.
Advanced Persistent Threats involve attackers quietly infiltrating cloud environments and remaining undetected for long periods. Their goal is usually to steal valuable data or monitor systems over time.
Organizations that fail to follow regulations such as GDPR, HIPAA, or PCI DSS may face legal penalties and reputational damage if sensitive data is not properly protected.
Business Email Compromise attacks occur when attackers impersonate executives or employees to trick others into transferring funds or sharing confidential information. These attacks can lead to direct financial losses, data exposure, legal liabilities, and damage to business reputation.
Enterprises often rely on external vendors and software providers. If a third-party system is compromised, attackers may use it as an entry point into the organization's cloud environment.
Many organizations struggle to maintain full visibility across their cloud infrastructure. Without proper monitoring tools, security teams may miss suspicious activities or vulnerabilities.
Employees sometimes start using apps or cloud tools without informing the IT team. Because these services are not officially approved or monitored, they may not follow the organization’s security policies and can introduce new security risks.
Cloud platforms often connect with third-party tools and services. If these integrations are not properly secured, attackers may exploit them to gain access to cloud resources.
Cloud security is built on core principles such as Zero Trust, least privilege access, and assumed breach. Best practices, including data encryption, network segmentation, shift-left security, continuous monitoring, and compliance alignment, help enforce these principles and protect enterprise cloud environments.
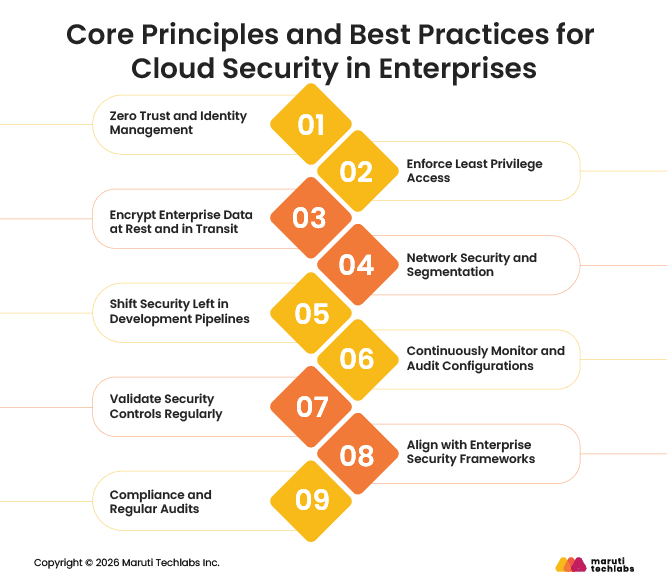
Cloud security today often follows the Zero Trust model, which means no user or system is trusted by default. Every access request must be verified. Identity and Access Management (IAM) helps control who can access cloud resources and what they can do. Practices like multi-factor authentication and strong identity checks help prevent unauthorized access.
Organizations should ensure that users and applications only receive the permissions required to perform their tasks. Limiting access in this way reduces the chances of attackers gaining control of sensitive systems if credentials are compromised. Regularly reviewing permissions and removing unnecessary privileges helps maintain stronger access control.
Sensitive enterprise data should always be protected through encryption. Data stored in databases, storage systems, or backups must be encrypted, and secure protocols should also protect data as it moves between services. Strong encryption standards help ensure that intercepted data cannot be easily accessed or misused.
Network security controls such as firewalls, private networks, and segmentation help isolate workloads and restrict unnecessary communication between systems. This limits the ability of attackers to move laterally across the cloud environment if a breach occurs.
Security should be integrated early in the development lifecycle. By adding security checks to CI/CD pipelines, organizations can detect vulnerabilities in code, infrastructure templates, and application dependencies before deployment. This approach helps prevent security issues from reaching production environments.
Cloud environments change frequently, so continuous monitoring is important. Tools such as AWS CloudTrail, Azure Monitor, and Google Cloud Security Command Center help track configuration changes, detect unusual activity, and identify potential security gaps. Regular audits also ensure that cloud resources remain properly secured.
Enterprises should regularly test their security controls to confirm that they work as intended. Security testing, simulations, and internal assessments help identify weaknesses and improve defensive strategies.
Organizations can strengthen their cloud security programs by aligning with established frameworks such as NIST, ISO, or CSA. These frameworks provide structured guidelines that help standardize security practices and improve governance.
Enterprises must ensure that their cloud environments meet regulatory requirements such as GDPR, HIPAA, or PCI DSS. Regular compliance reviews and security audits help organizations maintain regulatory readiness while improving their overall cloud security posture.
Enterprises adopt the cloud because it allows systems to scale quickly and handle changing workloads. As environments grow, security must evolve alongside them. Cloud security architecture helps by embedding security controls directly into the cloud environment, so the same protections apply as new resources are added.
Cloud platforms allow organizations to add or remove resources based on demand. A strong cloud security architecture ensures that security settings automatically apply whenever new resources are created.
For example, many organizations use Infrastructure as Code to create cloud infrastructure. Security settings can be included in these templates so that new servers, containers, or services follow the same security policies from the start. Identity and Access Management also helps control who can access these resources, which keeps systems secure even as the environment grows.
Resilience means that systems continue running even if something goes wrong. Cloud security architecture supports this by helping organizations build systems that can handle failures or security incidents.
Features such as backups, failover systems, and deployments across multiple regions help keep applications available. Monitoring tools also help detect unusual activity early so security teams can respond before issues affect the entire system.
Some security capabilities support both scalability and resilience in cloud environments. These include strong identity controls, automated security policies, network segmentation, and continuous monitoring. Together, these practices help organizations expand their cloud systems while keeping them secure and stable.
Cloud security is no longer just about stopping attacks. It is about designing systems in a way that limits the impact of any breach. Even if an attacker manages to enter the cloud environment, they should not be able to access sensitive data or critical systems. A well-planned cloud security architecture helps reduce these risks by controlling access, protecting data, and limiting how far an attacker can move within the environment.
Enterprises should also focus on building security into the way cloud systems are designed and developed. Security teams need to understand how cloud applications work so they can identify potential risks early. Using policy-as-code can further help by automatically checking configurations and guiding developers to follow secure practices. This approach helps organizations build cloud environments that remain secure as they grow and evolve.
Enterprises need the right expertise to build and maintain secure cloud environments. Maruti Techlabs helps organizations protect their infrastructure, applications, and data while supporting long-term growth. As an Amazon Web Services Advanced Tier Partner, we deliver tailored cloud solutions that improve performance, strengthen security, and support scalable digital transformation.
With strong experience in cloud architecture, security implementation, and migration services, we help enterprises design secure environments that reduce risks and improve operational efficiency. Our expertise spans cloud security and identity and access management, enabling organizations to control access, protect sensitive data, and maintain secure operations.
In one project, we helped a client migrate to AWS to improve infrastructure performance and reliability. The solution ensured zero downtime during peak loads, improved scalability, and strengthened security while reducing infrastructure and maintenance costs.
Talk to our experts about building a secure and scalable cloud architecture for your business.
To secure a multi-cloud environment, organizations should apply consistent security policies across all cloud platforms. Using centralized monitoring, strong identity and access controls, encryption, and automated security tools helps maintain visibility and protection across multiple providers such as AWS, Azure, and Google Cloud.
Secure cloud architecture helps protect sensitive data, reduce the risk of cyberattacks, and maintain regulatory compliance. It also supports system reliability and scalability. With the right security design, organizations can safely expand their cloud infrastructure while ensuring consistent protection across applications, users, and cloud resources.
Secure cloud architecture is the framework used to protect cloud data, applications, and infrastructure. It includes security controls such as identity management, encryption, network protection, monitoring, and compliance measures. These components work together to ensure that cloud systems remain protected from unauthorized access and cyber threats.
Cloud security architecture works by applying security controls across cloud environments. It manages user access, encrypts data, monitors activity, and protects networks and applications. These controls are built into the cloud infrastructure so that systems remain secure as new resources, applications, or users are added.
Organizations can implement cloud security architecture by defining security policies, managing user access, encrypting sensitive data, and monitoring cloud activity. Integrating security into development processes and using automated tools also helps detect vulnerabilities early and ensures security controls are consistently applied across cloud environments.
Cloud security architecture includes several components such as identity and access management, data protection, network security, application security, monitoring tools, and compliance controls. Together, these elements protect cloud systems, ensure secure communication between services, and help organizations manage risks across their cloud infrastructure.
Cloud security architecture focuses on protecting distributed and scalable environments. Unlike on-premises security, which relies heavily on physical infrastructure and network boundaries, cloud security uses identity controls, encryption, automated monitoring, and shared responsibility between the cloud provider and the organization.
Common risks include misconfigured cloud resources, weak access controls, insecure APIs, and a lack of monitoring. If not managed properly, these issues can expose sensitive data or systems to attackers. Organizations must regularly review security settings and follow best practices to reduce these risks.