

Role of AI in Cybersecurity: Practical Use Cases






Cyber threats are growing rapidly, and traditional security approaches are struggling to keep up. As attacks become more frequent and complex, organizations are looking for faster and more reliable ways to protect their systems.
This is where AI is making a clear impact. Around 94% of organizations believe it will drive major changes in cybersecurity, and adoption has already increased from 37% to 64%. This shift reflects how businesses are moving toward smarter, more proactive security strategies, including stronger fraud detection across industries like eCommerce, banking, and insurance, using AI.
AI helps spot unusual activity, detect threats as they happen, and respond quickly before they cause damage. It also makes it easier to focus on the most critical issues and reduces manual work. At the same time, attackers are also using AI to carry out more advanced attacks, which keeps the back-and-forth between defense and threat actors ongoing.
In this blog, we will explore how AI is transforming cybersecurity, its use cases, challenges, best practices, and what the future holds.
In 2026, AI is no longer just an extra layer in cybersecurity. It has become a regular part of how organizations protect their systems as threats keep getting faster and more complex. It helps teams handle large systems, catch risks early, and respond without wasting time.
There is also a clear shift in how security works. Instead of reacting after an attack, teams are trying to stay ahead of it. AI supports this by spotting possible threats early, so action can be taken before any real damage happens.
AI is also making security operations more efficient by reducing manual work and handling repetitive tasks. It can process huge amounts of data in seconds, identify patterns, and highlight what actually needs attention.
The following are some of the key roles AI plays in modern cybersecurity:
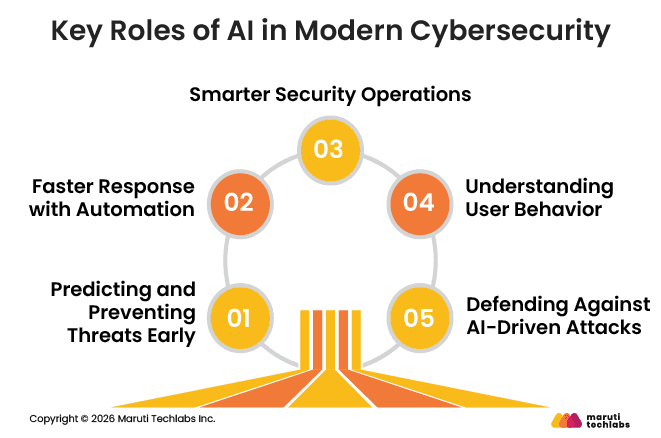
Overall, AI is changing how cybersecurity works by making it faster, smarter, and more proactive while also keeping up with evolving threats.
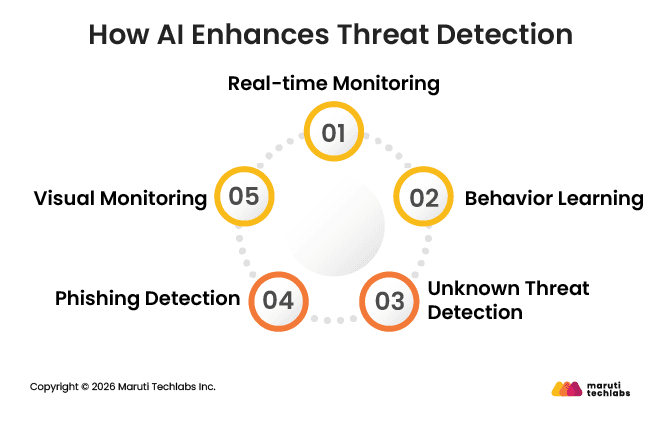
AI improves threat detection and incident response by using machine learning to process large volumes of data in real time. It identifies unusual activity and hidden patterns that traditional security tools often miss. This helps organizations detect threats earlier, reduce false alerts, and respond faster to potential vulnerabilities.
AI plays an important role in improving how organizations detect threats and identify risks early. It helps security teams monitor systems more closely and act before issues grow.
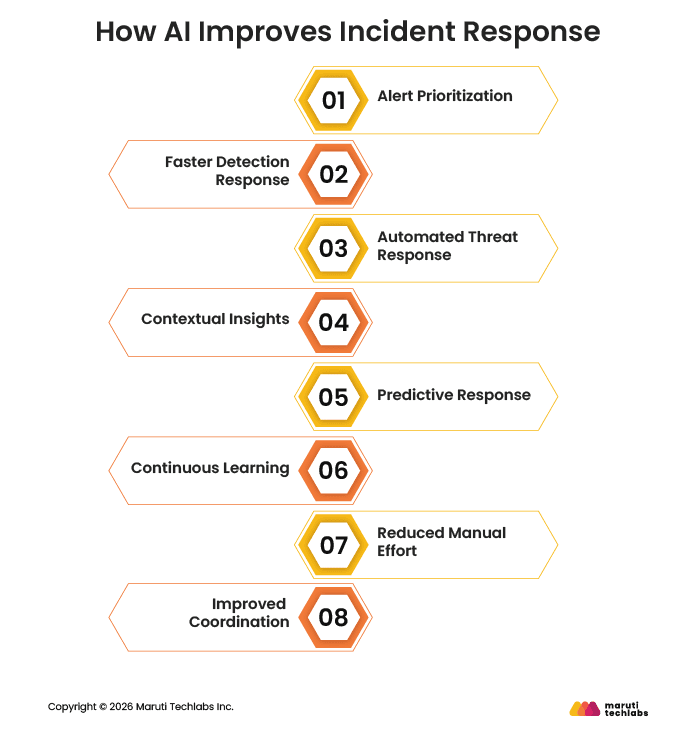
AI improves incident response by making the process faster, more automated, and more efficient during active cyber threats.
Recent cyberattacks show that even large companies are not fully safe. These incidents didn’t just affect systems but also caused real business losses and disruptions. They highlight why companies need stronger and more proactive security.
The Incident
Jaguar Land Rover was attacked after hackers got access using stolen login details. They used this to break into connected software and disrupt internal systems.
Data Breach Claim
The attack was more about breaking into systems than stealing large amounts of data, at least based on what was shared publicly.
Financial & Operational Impact
Factory operations stopped for weeks, which delayed production. The company faced heavy losses and a noticeable drop in revenue.
The Incident
Bybit was targeted by hackers who found a way to interfere with how transactions were approved. This helped them move funds without proper checks.
Data Breach Claim
This attack was focused on stealing money, not user data.
Financial & Operational Impact
A huge amount of cryptocurrency was stolen, making it one of the biggest crypto thefts. It also led to a rise in similar attacks across the industry.
The Incident
These retailers were hit by ransomware after attackers tricked employees into sharing access details. Once inside, they were able to disrupt systems.
Data Breach Claim
The main issue was system disruption, but there were concerns about possible data exposure as well.
Financial & Operational Impact
Online services were down for weeks, and supply chains were heavily disrupted, leading to empty shelves in stores. Marks & Spencer reported around a £300 million drop in profits, while both retailers faced major revenue losses and day-to-day operational challenges.
The Incident
Hackers targeted third-party tools connected to Salesforce and used them to access multiple company accounts.
Data Breach Claim
Data from several companies was accessed and taken during the attack.
Financial & Operational Impact
Many companies were affected, with over 200 organizations impacted in this supply chain hack. Salesforce and Gainsight faced disruption as teams relying on these tools had to pause work to fix the issue.
The Incident
Tata Technologies experienced a ransomware attack that temporarily affected its internal IT services. The attack forced the company to investigate and contain the issue quickly.
Data Breach Claim
The attackers claimed to have stolen a large amount of sensitive data, including business documents and project files.
Financial & Operational Impact
Client delivery operations remained unaffected, but internal IT services were briefly disrupted as the company brought in external experts to manage the issue. The attackers, linked to Hunters International, claimed a 1.4TB data breach involving sensitive files.
AI has become a regular part of how cybersecurity works today and helps teams detect threats faster, respond quickly, and manage systems more easily. At the same time, it also brings new risks as attackers use AI in their methods.
Here are seven use cases of AI in cybersecurity to know in 2026:
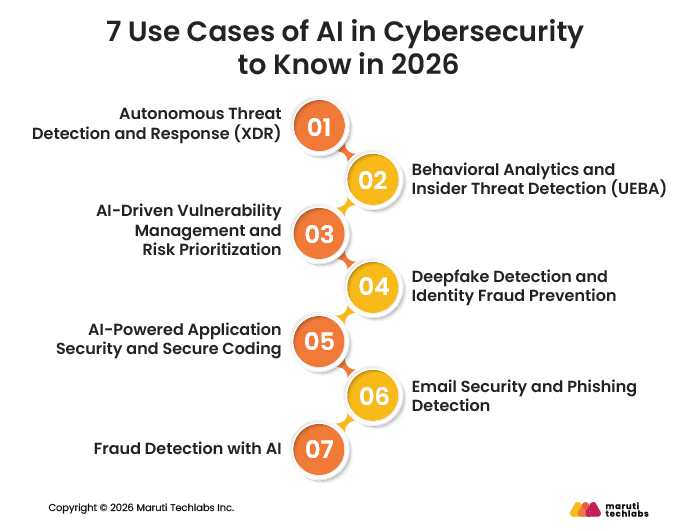
Usage
AI monitors systems, networks, and endpoints together to spot unusual activity. It connects different signals and identifies possible threats quickly.
Outcome
Security teams get fewer but more meaningful alerts. It also helps respond faster by isolating affected systems or blocking threats early.
Usage
AI scans systems to find weaknesses and studies which ones are most likely to be attacked. It focuses on real risks instead of listing every issue.
Outcome
Teams can fix the most important vulnerabilities first. This saves time and reduces the chances of serious attacks.
Usage
AI scans systems to find weaknesses and studies which ones are most likely to be attacked. It focuses on real risks instead of listing every issue.
Outcome
Teams can fix the most important vulnerabilities first. This saves time and reduces the chances of serious attacks.
Usage
AI analyzes voice, video, and user data to identify fake identities or manipulated content. It checks for inconsistencies that may not be obvious.
Outcome
It helps with fraud detection, especially in cases involving fake identities or deepfake scams. This improves trust and security in digital interactions.
Usage
AI helps developers while they write code by pointing out possible security issues. It also suggests better and safer ways to fix them.
Outcome
Problems are fixed early, before the code goes live. This reduces the chances of security issues later.
Usage
AI checks emails carefully to spot anything suspicious. It looks at how the message is written and whether it feels unusual.
Outcome
Even well-written scam emails can be caught. This helps protect users from falling for phishing attacks.
Usage
AI keeps track of how people usually make transactions. It quickly notices if something seems different or out of place.
Outcome
Suspicious transactions are flagged right away. This helps prevent fraud and reduces financial losses.
As AI is now a core part of how systems are protected as threats grow faster and more complex, many organizations are using it to detect issues early and respond without delays.
To make the most of it, companies are moving away from rule-based systems and focusing on smarter, automated workflows. The idea is to reduce manual work while improving how quickly threats are handled.
The following are some practical ways to implement AI in cybersecurity:
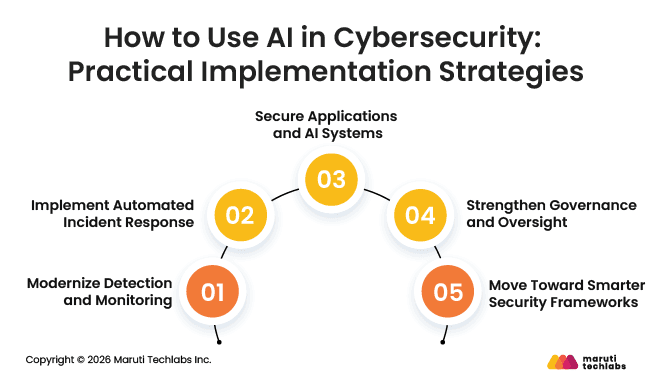
How it works
AI learns what normal activity looks like across users, devices, and networks. It also connects data from different sources to spot anything unusual.
Why it matters
This helps catch threats that older tools often miss and gives better visibility into what’s happening across systems.
How it works
AI can take action the moment a threat is detected, such as isolating affected systems or blocking suspicious access.
Why it matters
This reduces response time and limits damage, especially in fast-moving attacks like ransomware.
How it works
AI tools scan code while it is being written and check for possible security issues. They also help monitor how AI systems are being used.
Why it matters
This helps fix problems early and reduces risks linked to insecure code or AI misuse.
How it works
Organizations set clear rules for how AI should be used and keep human involvement in critical decisions.
Why it matters
This ensures better control and reduces the chances of errors or misuse.
How it works
Approaches like Zero Trust and behavior tracking verify users and systems continuously instead of trusting them by default.
Why it matters
This improves overall security and helps prevent unauthorized access.
While AI helps improve security, putting it into practice is not always simple. Many organizations face practical issues that affect how well these systems actually work.
Here are some common challenges:
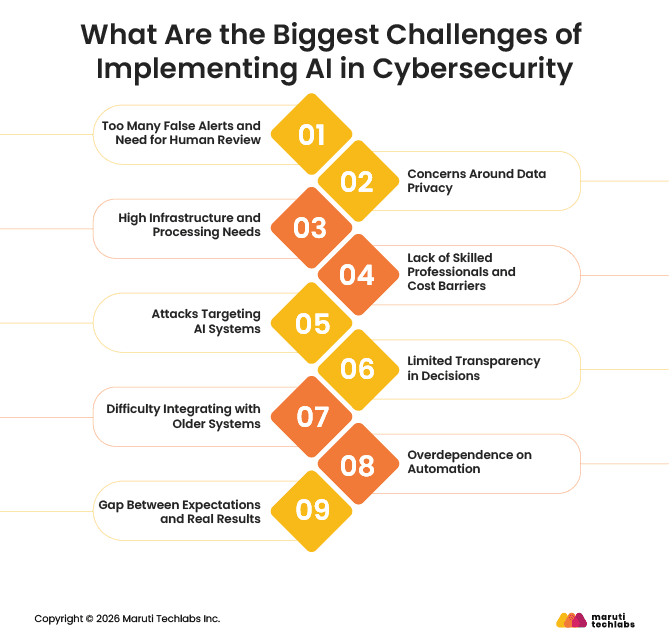
AI systems can sometimes flag normal activity as a threat. This creates extra alerts that teams need to check manually, which can slow things down and lead to alert fatigue.
AI relies on user and system data to detect unusual behavior. This raises concerns about how data is collected, stored, and used, especially with strict privacy regulations.
AI tools need strong systems to process large amounts of data. This means higher costs for computing power, storage, and ongoing maintenance.
There is a growing AI skill gap, with limited professionals who have the right expertise in AI for cybersecurity. Hiring and training such talent can be expensive, making it harder for many businesses to adopt and manage AI-driven security systems.
Hackers are also using AI and can manipulate AI models by feeding them misleading data. This can weaken detection and allow threats to go unnoticed.
Many AI systems work like a “black box,” where it is hard to understand how decisions are made. This makes it difficult for teams to fully trust or explain outcomes.
Connecting AI tools with existing security systems can be complex and time-consuming, especially when older technologies are involved.
Relying too much on AI can be risky. Without human checks, important decisions may go wrong or be misinterpreted.
AI is often seen as a complete solution, but in reality, it still needs time, testing, and proper setup to deliver consistent results.
Using AI in cybersecurity works best with a clear plan. It is not just about automation. Human involvement is equally important to keep things under control. This includes managing data properly, giving only the required access, testing AI systems for weaknesses, monitoring activity regularly, and training teams to handle new types of threats.
Here are seven best practices for implementing AI in cybersecurity:
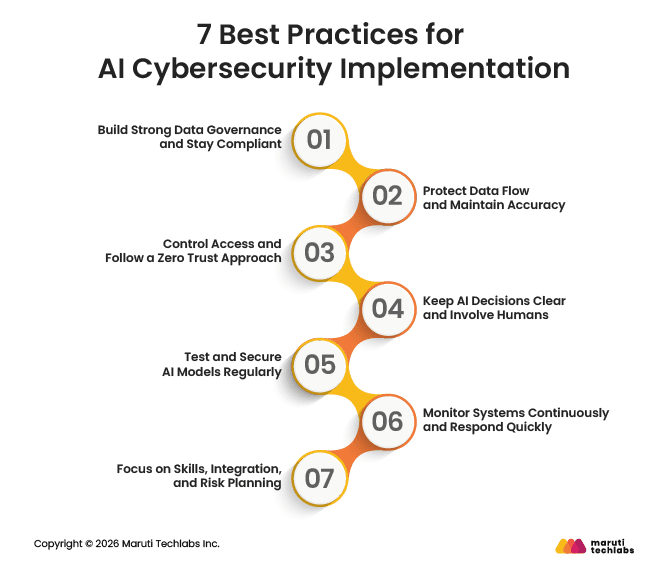
Make sure data is handled properly from the start by focusing on data quality and governance. Follow privacy rules and keep clear records of where data comes from and how it is used.
Secure your data at every stage, whether it is being stored or transferred. This helps prevent tampering and ensures AI systems work with reliable information.
Give users and systems only the access they need. Verify every request and use methods like multi-factor authentication to reduce risks.
AI should support, not replace, human judgment. Make sure teams understand how decisions are made and step in when needed.
Train AI systems to handle malicious inputs and test them for weaknesses. This helps reduce the chances of attackers manipulating the system.
Track system behavior in real time and set clear response plans. Quick action can limit damage when a threat is detected.
Invest in the right talent and make sure AI tools work well with existing systems. At the same time, assess risks regularly to avoid unexpected issues.
AI in cybersecurity is evolving quickly, and the next decade will bring some major changes in how organizations protect their systems.
AI is changing how organizations handle cybersecurity. It helps detect threats early and respond faster, which reduces risks and limits potential damage. Instead of waiting for attacks to happen, businesses can act in advance and stay better prepared.
At the same time, AI is not a complete solution on its own. It works best when combined with the right strategy, tools, and human involvement. Choosing the right AI-powered solutions plays a big role in how effective your security setup will be.
Every organization has different needs, so it is important to pick tools that fit your systems and goals. With the right approach, AI can make cybersecurity stronger, faster, and more reliable over time.
At Maruti Techlabs, we help businesses use AI in a practical way to strengthen cybersecurity without adding unnecessary complexity.
With 14+ years of experience, 250+ experts, and 100+ projects delivered, we build solutions that are reliable, scalable, and aligned with real business needs. Our team combines AI, data, and cloud expertise to help detect threats early, improve response time, and reduce overall risk.
We support a wide range of cybersecurity needs, including Data Security Services and Cloud Security Services, along with other essential security services. Our solutions also cover AI-driven threat detection and custom AI models through our AI Development Services, all designed to integrate smoothly with existing systems.
For example, we helped an image protection platform improve image theft detection accuracy from 65% to 88% and reduce manual effort by 66%, leading to faster case resolution and better user experience.
AI is used in many parts of cybersecurity, including threat detection, fraud prevention, email protection, and user behavior monitoring. It looks at data from networks, devices, and users to spot unusual activity. This helps teams reduce manual effort and respond to risks more quickly.
AI helps organizations detect and respond to threats faster. Instead of reacting after an attack, teams can identify risks early and take action sooner. It also learns from past incidents and offers insights that help prevent similar issues in the future.
AI algorithms help identify patterns, detect unusual behavior, and predict potential threats. Machine learning models are commonly used to analyze activity and flag anything suspicious. They can handle large volumes of data and often catch threats that traditional rule-based systems miss.
AI predicts cyber threats by analyzing historical data and current system activity. It looks for patterns linked to past attacks and identifies similar signs in real time. This helps organizations take preventive steps before an attack happens, reducing the chances of damage.
There are many AI-powered tools used for threat detection, endpoint protection, and network monitoring. These tools analyze data, detect suspicious behavior, and automate responses. They help improve visibility across systems and reduce the time needed to identify and handle security incidents.
Traditional cybersecurity follows fixed rules and looks for known threats. AI takes a different approach. It learns from data and keeps improving over time. This helps it spot new and unknown threats by picking up on unusual behavior, making it more flexible for handling modern risks.
AI doesn’t replace people, it supports them. It takes care of repetitive tasks and helps spot threats faster. But human expertise is still essential for making decisions, handling complex issues, and guiding the overall security strategy. The best results come from using both together.
AI supports many areas of cybersecurity, including threat detection, incident response, fraud detection, email security, and user behavior monitoring. It helps organizations improve visibility, respond faster, and reduce risks by analyzing data and identifying potential threats across systems.


